
In recent weeks Fujitsu’s Advanced Threat Centre (ATC) has been tracking the rapid developments in cyber security threats related to COVID-19 and specifically the influx of associated malware and phishing scams.
As we seek to play our part in helping society during this time of global flux I would like to share some of our expert insights into the malicious activity our ATC have observed to help you, our customers and partners, maintain a secure posture during these unprecedented times.
The global spread of the COVID-19 and its impact on business models and working practices has presented both unscrupulous cybercriminals and state actors with a new and topical trend to leverage in order to increase the probability of successfully exploiting targets through fear and misinformation.
Thousands of new potentially suspicious domains are being created every day and there has been a large shift towards phishing campaigns exploiting the public’s thirst for information related to the pandemic.
Furthermore, as many organizations have quickly had to switch to home-working practices, it is likely that personal computers and mobile devices are being utilized to complete business tasks. These devices may not have the same levels of security that corporately managed devices may have which opens up a new attack surface for cybercriminals.
It is vital that organizations stay up-to-date with the very latest threats and can prepare themselves to respond to these appropriately to protect their customers and staff.
Below is a summary of some of the key trends our Threat Intelligence experts have already observed and expect to see increase.
Phishing scams
The most prevalent threat we have identified is that of phishing campaigns that are seeking to leverage the focused attention on the topic of COVID-19 and use that to compromise or extort individuals and companies.
We have identified numerous phishing campaigns that are leveraging the heightened global awareness and sensitivity to COVID-19, and this trend is being observed across the industry. The campaigns we have observed are centred around emails looking to provide Coronavirus updates, provision of safety masks, vaccine information and even posing as organizations looking for donations to charitable relief funds.
These attacks have had a number of different objectives, from simple phishing techniques to harvest user login details with a view to using them in further malicious activity or to sell on, through to malware delivery attacks that install spyware, infostealers or trojans on systems in order to capture user interactions, steal sensitive data or utilise the machine as part of a bot network.
The below example highlights just how far cybercriminals are willing to go in exploiting the current situation. Rather than preying on emotion or fear, this campaign attempts to extort money from recipients by way of appealing to their charitable nature, playing to a human desire to help, with the lure of donating to the World Health Organization to assist with the ongoing pandemic.
Phishing Email Content
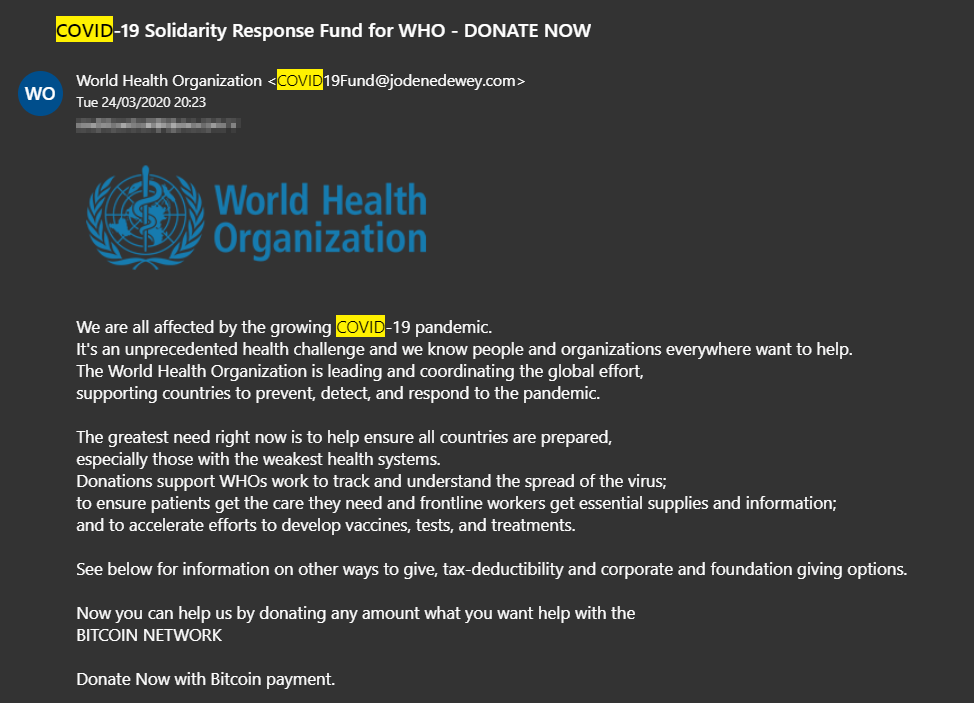
From a very superficial glance this email looks genuine however, there are key features that indicate that it is not legitimate:
- The sender does not have a World Health Organization (WHO) email address – COVID19Fund@jodenedewey.com
- An email directly from the WHO is unlikely to use such direct language in the subject line – COVID-19 Solidarity Response Fund for WHO – DONATE NOW
- The email asks for donations in Bitcoin which the WHO is very unlikely to want.
Fraudulent free services
Our experts also expect to see a rise in the number of malicious applications offering services such as Video Conferencing, Training Platforms and Food Delivery, thanks to the rise in popularity of these services. Any service that has seen an increase in demand due to COVID-19 will no doubt be used by cybercriminals as an opportunity to create malicious schemes offering these services for free.
Scam services are likely to try and obtain bank details, personal information and could even harbour malware. This type of activity has already been reported in the press related to two of the most popular content streaming services.
Whenever free services or apps appear they should be thoroughly scrutinized by checking third-party reviews to understand the legitimacy of these new services before using them.
Increased Domain Name registration of suspicious Coronavirus websites
The UK's domain name registrar Nominet, which manages the launch of .uk websites, is stepping up efforts to tackle the proliferation of sites dedicated to scamming the public, for example by selling fake vaccines, protective equipment and remedies to the COVID-19 virus.
Rather than taking down domains after they have been reported as malicious, the organization has implemented more radical measures to stop these sites appearing in the first place, with extra scrutiny of websites names containing "coronavirus", "covid", or other selected terms related to the pandemic.
Business Email Compromise (BEC) Scams switch to online gift cards
Scammers behind business email compromise (BEC) attacks have adjusted their tactics to match the current situation given the tens of millions of employees working from home during the COVID-19 outbreak.
Ordinarily, they would attempt to convince victims to buy gift cards as a quick favour to one of their company's executives but scammers have now switched to asking them for digital gift cards since physical stores are now either closed or a lot harder to reach due to lockdowns.
Increasing fraudulent activity related to Tourism and Travel
With holidays and flights continuing to be cancelled, it is likely that scams will emerge offering compensation or reimbursing money due to travel disruption. Education surrounding what malicious emails look like can reduce the risk that phishing campaigns pose. People should never feel pressured into providing personal information; when faced with emails such as ‘Travel Compensation Offer Expires in 12 Hours’, cybercriminals want victims to act first and think later.
Mitigate the impact of COVID-19 related threats
The vast majority of malicious COVID-19 communications occur as unsolicited emails. We at Fujitsu stress the importance of never interacting with links or attachments included within emails sent from unknown external contacts. Use internet browsers to search for legitimate information sources such as the World Health Organisation or the UK National Health Service when collecting advice regarding the COVID-19 outbreak.
Numerous malicious phishing campaigns exist pretending to be from legitimate services, so we emphasize the importance of never interacting with emails even if they appear to be legitimate.
Furthermore, ensuring that software is kept up to date and that the latest software patches have been installed can, in many cases, limit the influence that malware can have on a compromised machine. Malware strains often use software vulnerabilities to maintain persistence and secrecy on infected systems.
Utilizing automatic updates allows security updates to be installed upon release by software vendors, further reducing the chance that malware can exploit software vulnerabilities.
Expert support against Advanced Threats
To defend against these threats during the current crisis, Fujitsu’s Advanced Threat Centre provide an enhanced overlay to the security services we provide in an attempt to reduce the potential impact this activity could have on our customers and their businesses.
We gather and disseminate Threat Intelligence on COVID-19 related scams to enable activities such as the proactive blocking of known bad URLs in web security technologies and the creation of threat feeds in SIEM to enable the detection of certain events.
Find out more about what we can do to keep your business safe and secure on our website.












